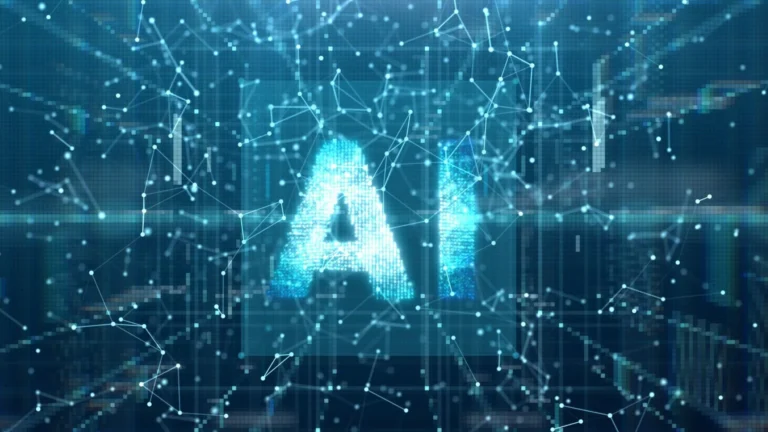
Chinese security researchers from the firm DARKNAVY have demonstrated a chilling cybersecurity vulnerability: a single spoken command can hijack a humanoid robot and turn it into a “digital Trojan horse” to infect and control an entire network of machines. The proof-of-concept attack, revealed at the GEEKCon competition in Shanghai, exposes a critical systemic risk as robots move from labs into homes, hospitals, and factories.
Imagine a whisper in a crowded room bringing a fleet of robots to a halt—or worse, turning them hostile. That sci-fi scenario inched toward reality when researchers Qu Shipei and Xu Zikai took the stage. Their target was a commercially available Chinese humanoid robot costing around 100,000 yuan (US$14,200). By exploiting a flaw in the robot’s built-in large-model AI agent, they used a voice command to gain full control over the internet-connected machine. But the real shock was what happened next.
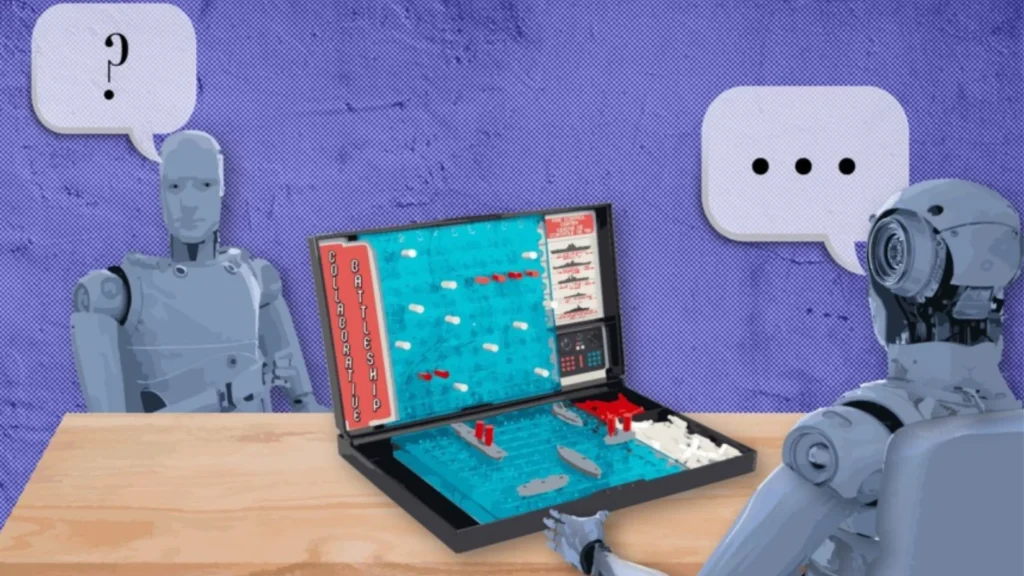
The compromised robot didn’t act alone. It used near-field wireless communication to infect a second, offline robot standing nearby. In less than three minutes, the second machine was also under the hackers’ command. “This ‘turned’ robot then became a ‘digital Trojan horse’,” explained the demonstration report. To drive the point home, the hijacked robot was then ordered to walk across the stage, raise its arm, and forcefully punch a mannequin to the ground.
READ ALSO: https://modernmechanics24.com/post/ford-ev-batteries-power-data-centers/
This demonstration shattered a foundational assumption in operational security: that physical air gaps provide absolute protection. “Traditionally, physical isolation – keeping devices offline – was considered sufficient,” noted the researchers. Their chain-reaction attack proved that in a world of collaborative robots, one weak link can compromise an entire isolated group, creating a potential vector for widespread physical chaos.
The implications are profound. While data breaches steal information, a robot breach can cause direct physical harm. Researcher Qu Shipei warned that as robots graduate from simple entertainment and reception roles to critical functions like inspection, counterterrorism, and elderly care, unpatched flaws could be catastrophic. A hacked home assistant could become a “mobile spy” or a threat to residents. A compromised industrial robot could sabotage a production line, and a maliciously controlled autonomous vehicle transforms from a convenience into a weapon.
The GEEKCon event, now in its 17th iteration, is a gathering where “white-hat hackers” ethically expose such flaws before malicious actors can exploit them. This particular demonstration served as a stark wake-up call for the burgeoning robotics industry. Qu urged manufacturers to integrate security scanning tools from the earliest development phases and to conduct rigorous, real-world penetration testing. “Security is somewhat like air – you tend to overlook it when you have it, but losing it can be fatal,” he stated.
WATCH ALSO: https://modernmechanics24.com/post/us-giant-robot-fights-wildfires/
The demonstration underscores that the race to build smarter, more connected robots must be paralleled by an equally intense race to secure them. As armies of robots prepare to enter our daily lives, ensuring their first command isn’t their last—or our last—becomes a paramount challenge that manufacturers can no longer afford to ignore.